What is DNS amplification attack?
If you’re familiar with the internet, you’ve probably heard of cyberattacks, but one that might not be as well-known is the DNS amplification attack. It’s a type of Distributed Denial of Service (DDoS) attack that can cause major disruptions to websites and online services. In this article, I’ll explain what it is, how it works, and why it’s so dangerous, all in simple terms.
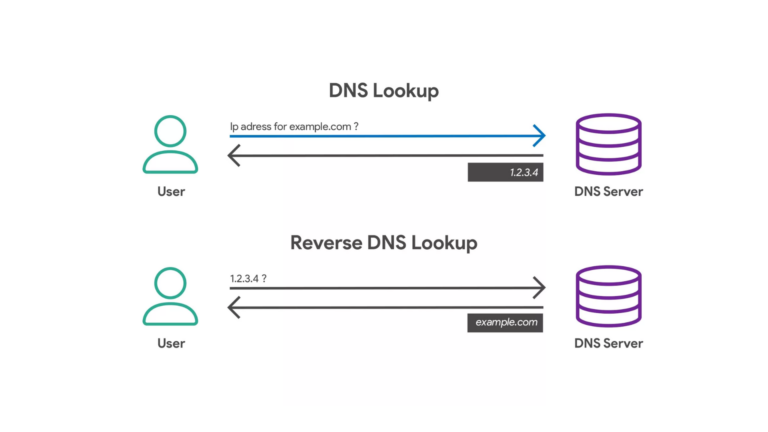
What Is DNS?
Before diving into the attack itself, let’s take a quick look at DNS, which stands for Domain Name System. Think of DNS as the internet’s phonebook. When you type a website address (like www.example.com) into your browser, DNS helps translate that address into an IP address that computers can use to communicate with each other.
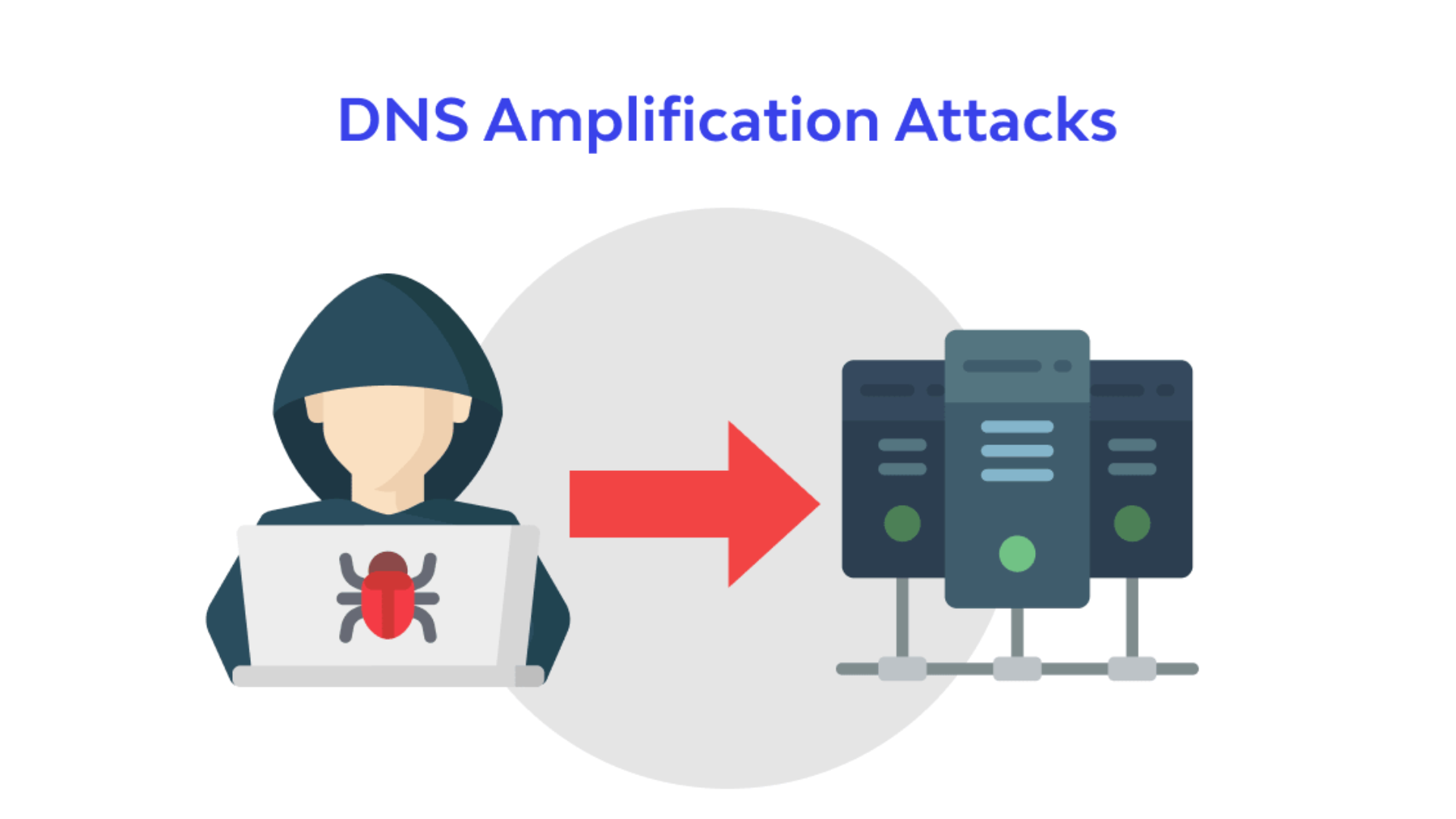
What Is a DNS Amplification Attack?
A DNS amplification attack is a type of DDoS attack where the attacker tricks DNS servers into sending large amounts of data to a victim’s server, overwhelming it and causing it to crash or slow down. The goal is to make a website or online service unavailable to users.
Here’s how it works:
- Spoofing the IP Address: The attacker sends a request to a DNS server, but they “spoof” the request to make it look like it’s coming from the target’s IP address (the victim). This means the server will send the response to the victim, not the attacker.
- Amplification: The DNS server responds with a much larger amount of data than what was sent in the initial request. This is where the “amplification” part comes in. The attacker uses this to their advantage, sending a small request that results in a large response, multiplying the amount of data sent to the victim.
- Overloading the Target: Since the victim is receiving so much unexpected data, their server gets overwhelmed. This causes the website or service to slow down or crash, making it inaccessible to users.
Why Is It Dangerous?
- Massive Disruption: A DNS amplification attack can flood a victim’s server with millions of requests, making it nearly impossible for legitimate users to access the service.
- Hard to Trace: Since the attack involves spoofing the source IP address, it’s difficult to track down the attacker.
- Easy to Launch: DNS amplification attacks are relatively easy to carry out. Attackers don’t need a lot of resources or special skills; they can exploit open DNS servers that are not properly secured.
Real-World Examples
There have been several high-profile cases of DNS amplification attacks over the years. One notable example is when the attacker launched an attack that flooded a website with over 500 gigabits of data per second. This caused massive slowdowns for that website and made it nearly impossible for users to access the site.
How to Protect Against DNS Amplification Attacks
If you’re running a website or a server, here are a few steps you can take to protect yourself from DNS amplification attacks:
- Use DNS Security Features: Implement security measures like DNSSEC (DNS Security Extensions) to prevent attackers from manipulating DNS records.
- Limit Response Size: Configure your DNS server to limit the size of responses it sends out. This reduces the chances of amplifying attacks.
- Block Unnecessary DNS Queries: If you’re not running a public DNS service, make sure your server isn’t accepting queries from random users on the internet.
- Use Anti-DDoS Services: Many hosting companies and cloud providers offer DDoS protection services that can help prevent large-scale attacks.
- Monitor Traffic: Keep an eye on the traffic to your server. If you notice unusual spikes, it could be a sign of an attack.
Conclusion
A DNS amplification attack is a powerful and potentially disruptive type of cyberattack that targets DNS servers to flood a victim’s server with unwanted traffic. While these attacks are relatively simple to carry out, they can cause a lot of damage if proper precautions aren’t taken. By understanding how DNS amplification works and taking steps to protect your servers, you can reduce the risk of falling victim to this kind of attack.